RISE ABOVE WITH ALTVIA.
Our leading alts platform simplifies data complexity, streamlines capital raising and deployment, and delivers a modern LP experience. As your needs evolve, we help you adapt – turning relationships and opportunities into preferred returns, strong investments, and lasting partnerships – helping you rise above the competition.
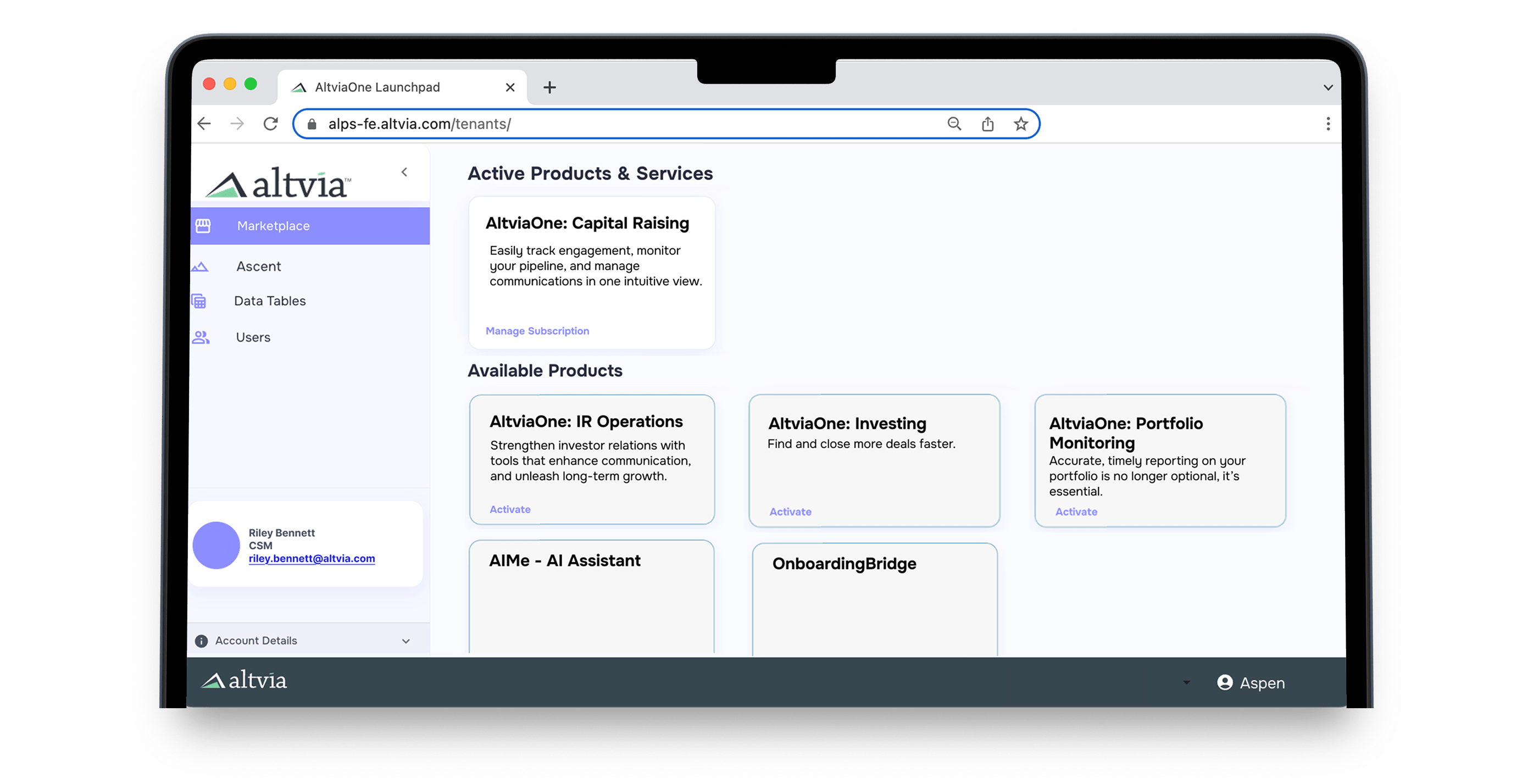
An End-to-End Platform for Peak Productivity
Get access to a full platform without having to buy multiple one-off point solutions and products to achieve your business goals.
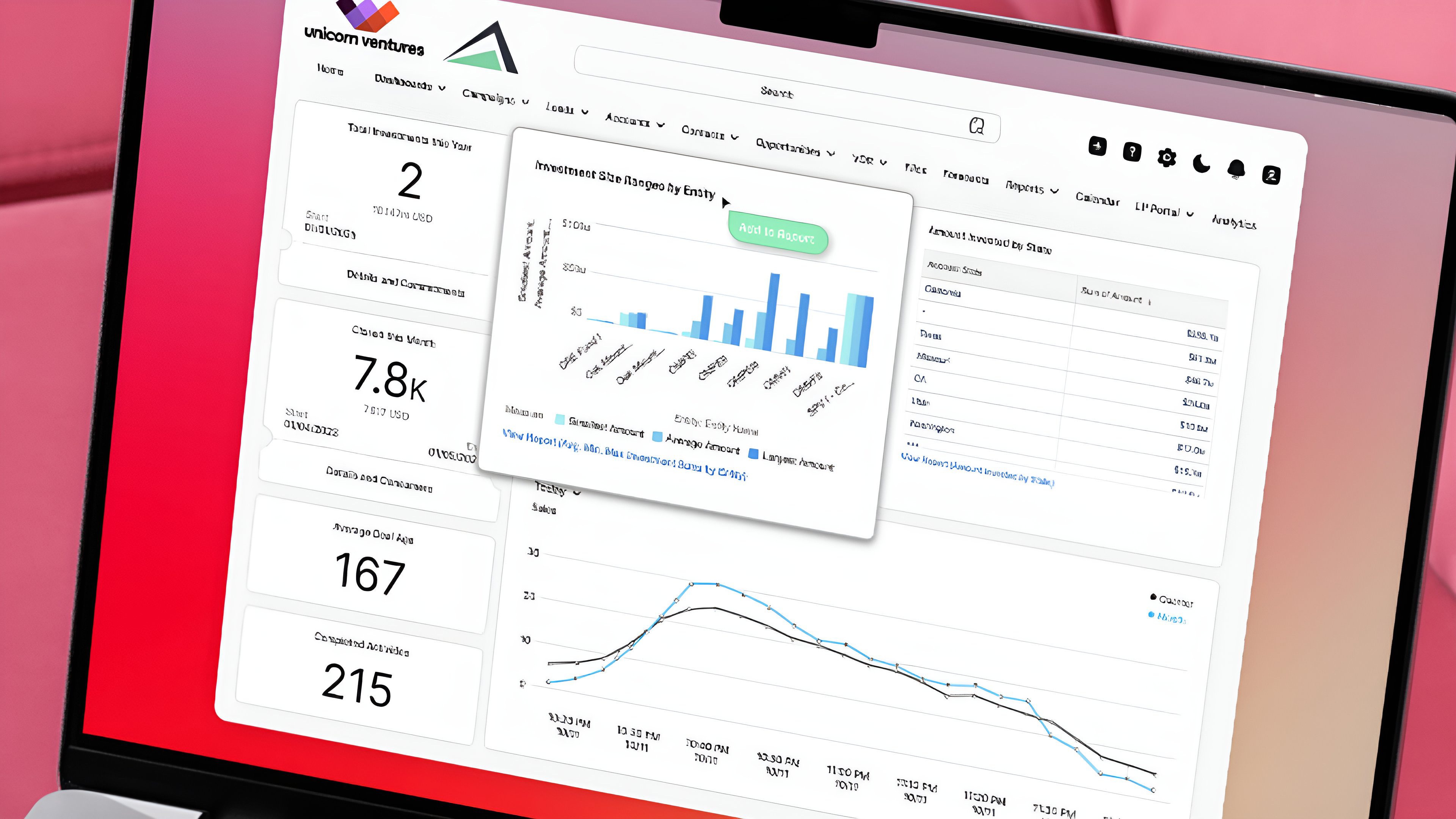
CRM
An incredibly simple to use CRM purpose-built for firms who want to grow private capital relationships and close deals.
VDR & Portal
Deliver a best-in-class LP experience with our innovative portal & VDR that make data presentation a compelling story.
Insights
The demand for swift and accurate reporting is paramount. Analyze deal, fund, and relationship data with precision in minutes.
CRM
- Be ready for Monday morning with accurate data at your fingertips.
- Know exactly where your fundraising and deal pipeline stand at any given moment.
- Quickly access key details about existing and prospective investors.
- Focus on the most impactful deal sources with a streamlined, data-driven approach.
- Send tailored messages to key stakeholders for increased engagement.
- Streamline the creation and distribution of capital calls, PPMs, and updates for timely, accurate communication.
- Facilitate collaboration across your team for faster decision-making.
VDR & Portal
- Safely share sensitive documents with the right stakeholders.
- Create a secure, branded experience that reflects your firm’s identity in the digital space.
- Tailor messages and updates to your investors, improving engagement and trust.
- Easily manage and segment your data to target the right investors and stakeholders.
- Real-Time Performance Updates: Provide your investors with up-to-the-minute performance insights, enhancing transparency.
- Facilitate collaboration across your team for faster decision-making.

Insights
- Ensure your firm’s data is clean and accurate, reducing errors and increasing reliability.
- Access key insights without wasting time in emails, spreadsheets, or disconnected tools.
- Effortlessly upload and integrate unstructured data into your tech stack for greater efficiency.
- Gain access to comprehensive analytics and reporting to make informed, strategic decisions.
PLATFORM
Key Features & Benefits For A Seamless Experience
The most modern user interface, driven by AI, to ensure your platform actually gets adopted.
CRM
Empower Your Team With Award-Winning Relationship Management Tools
Unite all of your firm data, tools, and teams on a single customer platform.
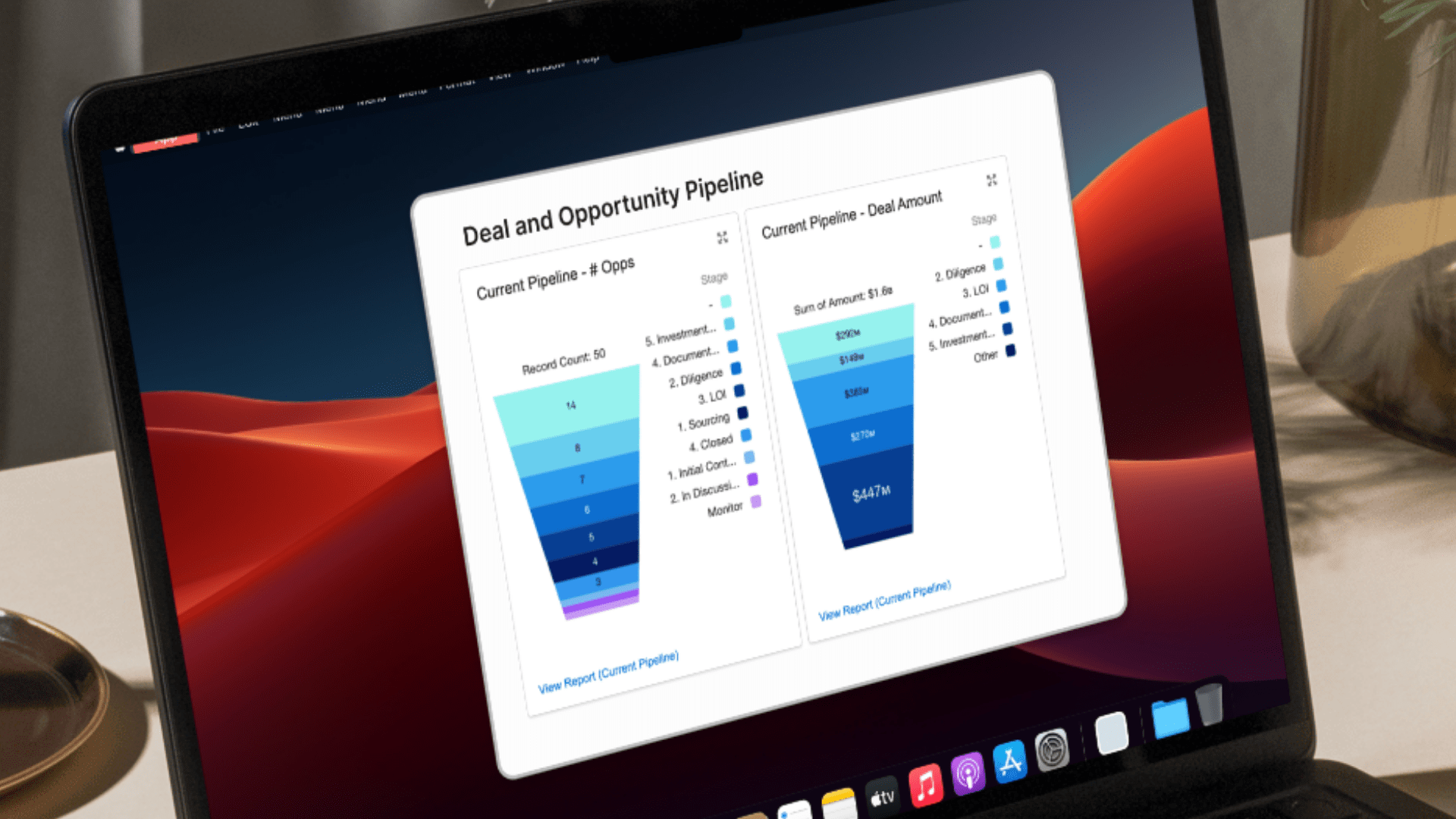
- Pipeline Management
- Investor Activity Tracking
- Lead Management & Prospecting
AI
The Only AI Built for Private Capital Markets
AI isn’t just about automation; it’s about solving specific problems with precision to drive productivity gains. Leverage our AI Assistant, AIMe, and proprietary AI Agents, to do more, faster.
- AI Assistant
- AI Agent: Sentiment
- AI Agent: Research
SHARESECURE
Digital Investor Experience
In today’s competitive market, proactive engagement with investors sets you apart. Strengthen investor relationships with tailored updates that enhance communication, and unleash long-term partnerships.
- Data Room
- Smart Data & Document Segmentation
- Firm Branded LP Portal
- Generate Custom Templated Reports
CORRESPOND
Redefining Marketing Standards with
Exceptional Features
Engage investors faster, raise capital more efficiently, and scale with ease, minimizing time spent on admin tasks and workflows.
- Design and send marketing emails at scale.
- Securely send capital calls to investors.
- Safely distribute PPMs with potential investors.
- Send correspondence to LPs across multiple entities.
REPORTING
Flexible & Fast Business Intelligence, Data Analysis & Reporting
Eliminate manual and error-prone procedures, enhance data transparency, enable deeper insights and flexibility for informed and strategic decision-making.
- Standardized Insights embedded in CRM and Portal
- Portfolio Management
- Intuitive Data Visuals
- Event Management (Roadshows)
Schedule a Demo ➔
You’ll be amazed at what Altvia can do for you and your team. Let’s talk and see how we can help.
Pick a Meeting Time
Fill out the form below with your work email to be routed to a calendar to select your meeting time.
